¶ Single-Interface Cyber Gateway
Adjacent to the internal applications running in a public cloud, data center, or on-premises server, Exium places a small piece of software called Cyber Gateway (CGW), deployed as a VM or bare metal, which is used to extend a highly secure Zero Trust Path out to the Intelligent Cybersecurity Mesh.
CGW deployment is required for Secure Private Access and SD-WAN services. Once the CGW is deployed, our zero-trust network access capabilities can be configured to enable access to the apps in the public cloud, data center, or on-premises server.
We can help you determine where you should deploy the CGW in your environment.
¶ Technical Requirements
The CGW can be deployed on Hardware, VM or Public Cloud. For VM or Public Cloud deployment, we recommend a 1-vCPU machine with at least 1 GB RAM for initial testing. In production environments, resources allocated for the Cyber Gateway can be scaled, based on the bandwidth requirements.
|
vCPU |
RAM |
HDD |
Type |
OS |
Supported Bandwidth |
|---|---|---|---|---|---|
|
1 |
1GB |
30GB |
VM / BM |
Ubuntu |
Up to 400 Mbps |
¶ Create the Cyber Gateway
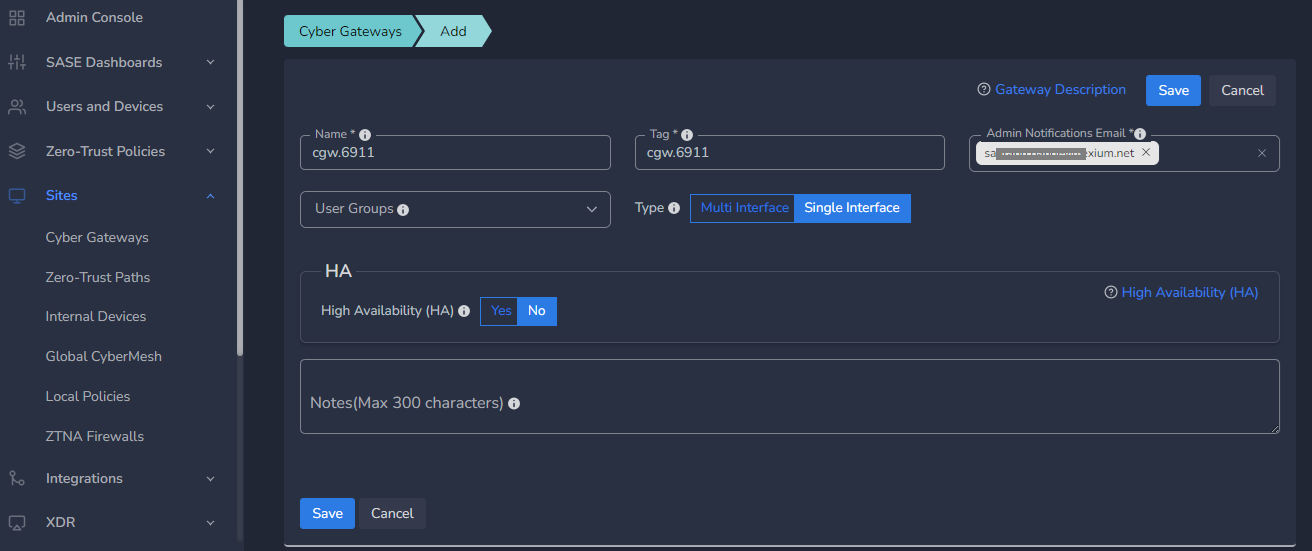
The first step in deployment is making sure that you have the Ubuntu latest version iso or image for the cyber gateway deployment. To create a Single-Interface Cyber Gateway (CGW-SIF), follow the steps below.
- Navigate to the MSP admin console -> Client Workspace
- Click on Sites in the left menu bar → Add Gateway
- Make sure Single-Interface is selected
- Enter a Name for the cyber gateway, admin email to receive notifications or alerts
- Select User Groups if already created or skip if no there is no additional requirement, admin can add/delete user group association later also.
- Select HA yes, in case high availability is required
- Click Save
¶ Deploy the Cyber Gateway
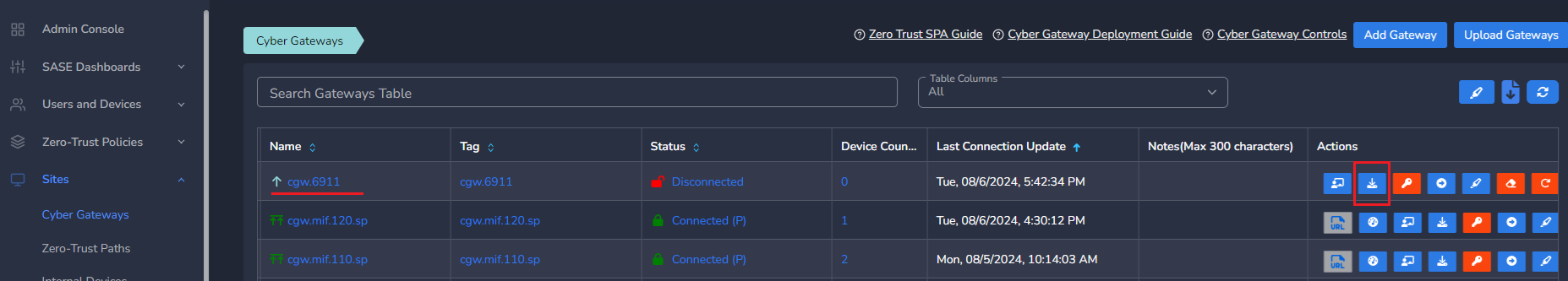
- Copy the install command for the cyber gateway you just created as shown in the screenshot below
- Paste the install command in the machine's SSH console/terminal
- Press Enter
In case, you are unable to login to machine using SSH to copy and run CGW install command, then we recommend you to run pre-install script mentioned below. You have to type it on console, because copy paste won't work on some direct machine consoles.
bash <(curl -s https://s3-api.speerity.net/cgw/scripts/cgwctl.sh)Please share Workspace and CGW names with us on support@exium.net. We will push installation remotely.
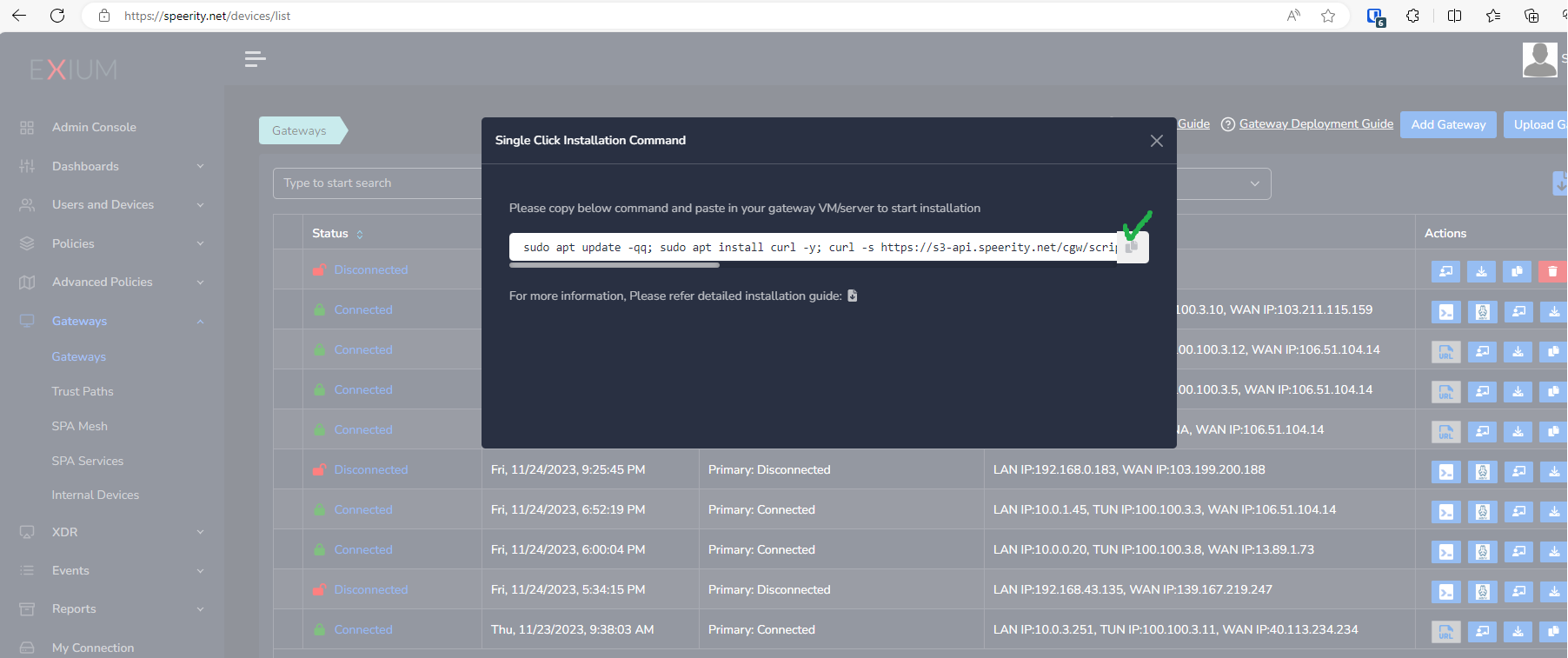
The CyberGateway deployment will start. At this time, you can leave the deployment running unattended. You will receive an email on the admin email that you specified earlier when the deployment is complete. You can also check the status of the cyber gateway in the Exium admin console. When cyber gateway is deployed successfully and connected, you will see a Green Connected Status as in the screenshot below.
Post successful deployment, subnet of the CyberGateway machine's interface will be added as a Trustpath automatically. It will be associated to “workspace” group category, i.e. all the users in workspace will be able to access the resources on that private subnet. You can edit group association any time as per requirement. You may create new user groups and associate them with the trust path.
Once the CyberGateway is deployed successfully and connected, you can start testing the Zero Trust Secure Private Access policies.
Additional trust paths can be added manually. In case additional trust paths have different next hops, then those can also be configured from admin console. In case additional trust path subnets are already accessible via Cybergateway's default gateway then next hop configuration is not required.
You can follow below steps to add additional trust path subnets with or without their next hop.
- Click on Zero-Trust Paths
- Select CyberGateway from drop down list
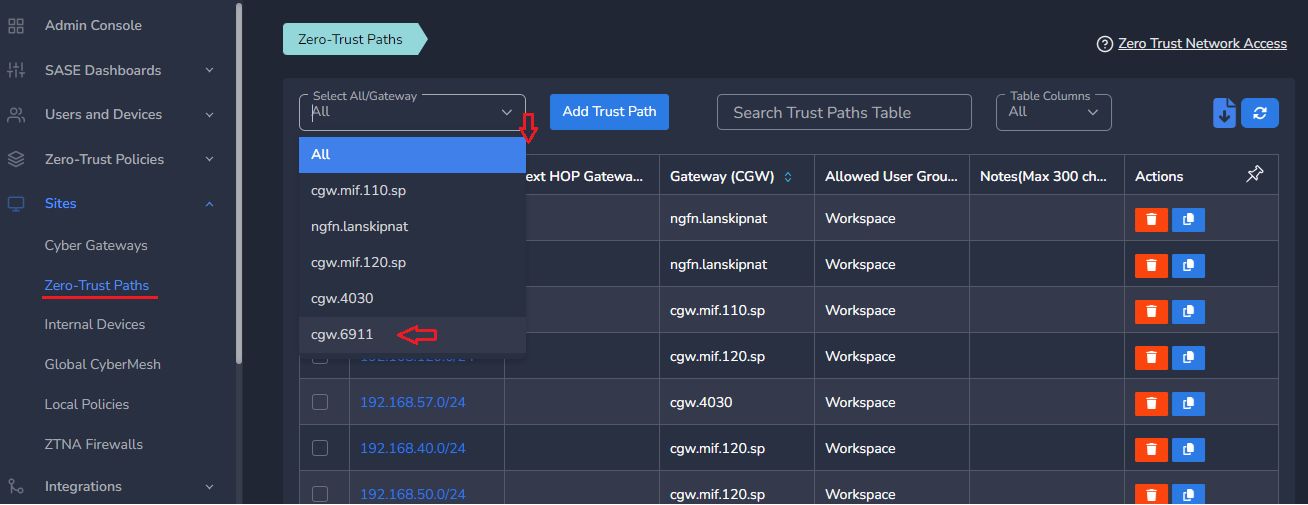
- Click on Add Trust Path
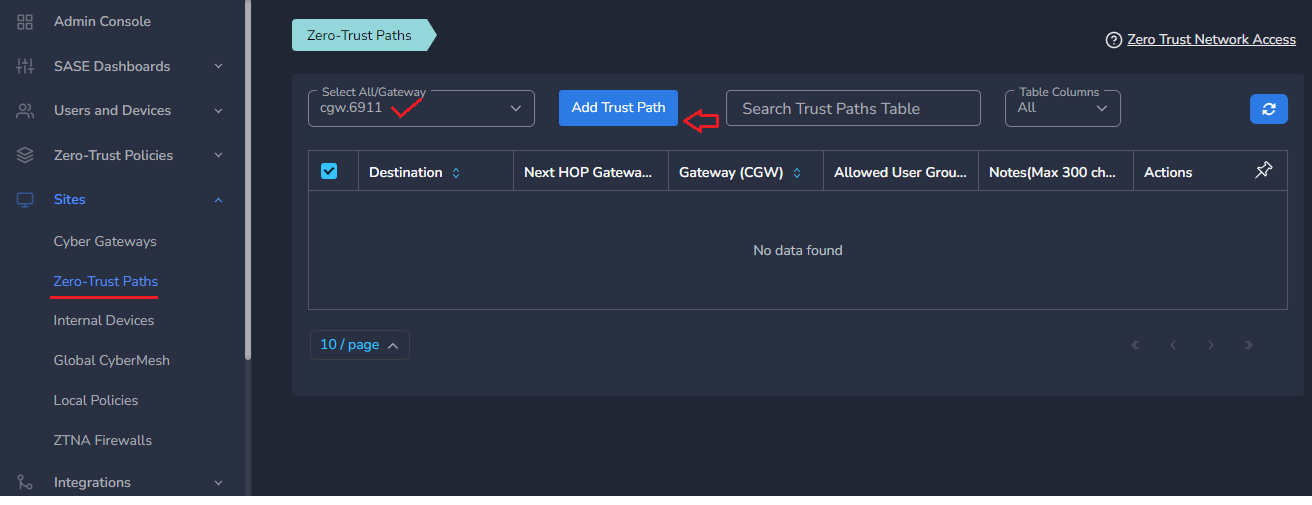
- Provide Network Destination or private subnet to allow access for remote users
- Provide Next HOP Gateway IP, if it is different from default gateway of CyberGateway machine
Make sure next hop gateway IP is accessible from CyberGateway machine, else route configuration will fail
- Select Allowed User Groups or leave workspace group associated in case whole organization is allowed to access that subnet
- Save the configuration [CGW will pull configuration, and routes will be added after few mins.]
- Additional trust path configuration can be modified later as per requirement or when the next hop changes
Do not add next hop configuration in the default trust path which is created automatically by CyberGateway post deployment.
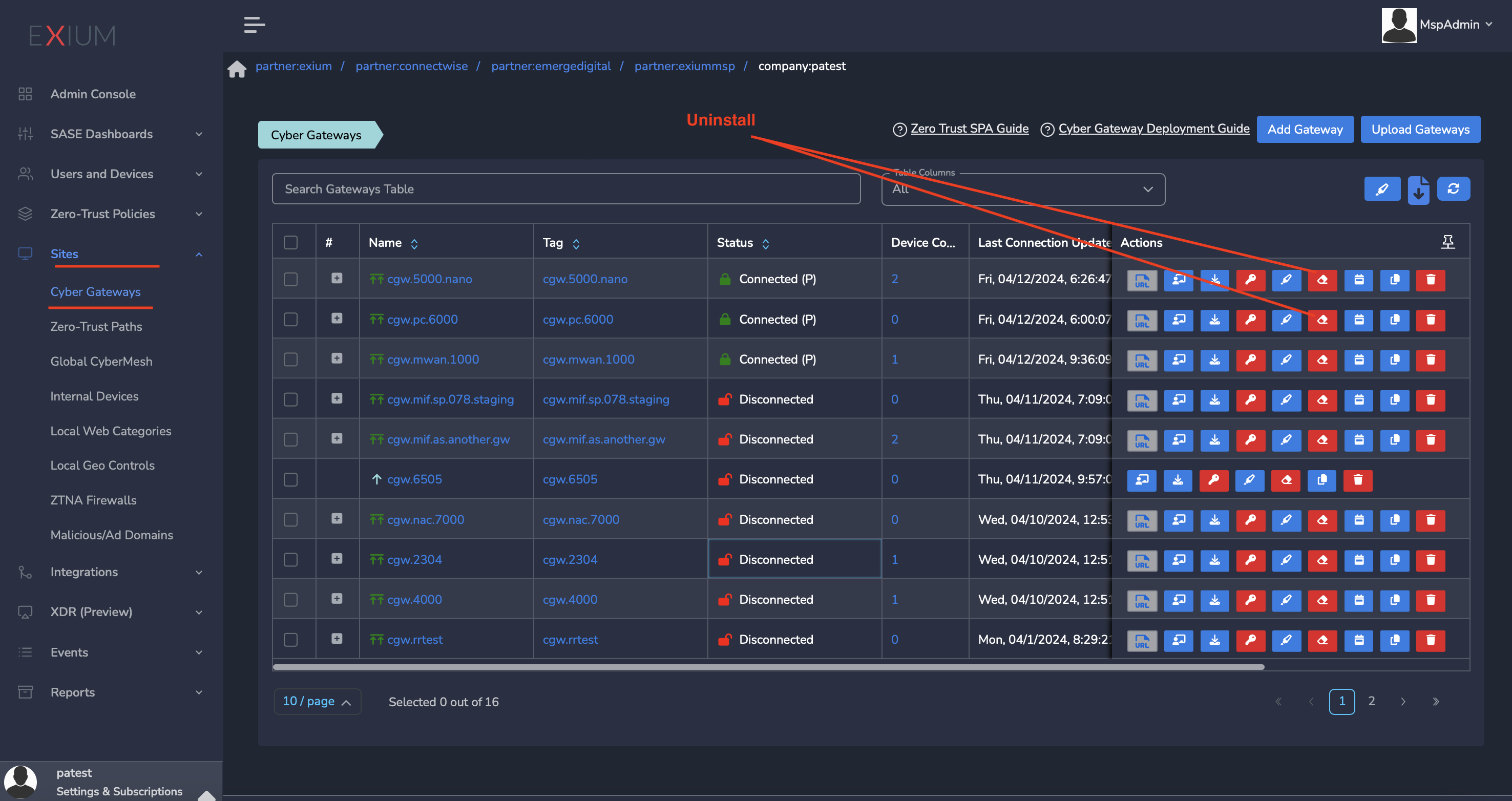
¶ Uninstall CyberGateway
Uninstall can be done from admin console or using CGW CLI commands
¶ From Admin console
- Navigate to the MSP admin console -> Client Workspace
- Click on Sites → Cyber Gateways in the left menu bar
- Select the CyberGateway you want to uninstall and click on the icon show in screenshot
- It will take around 5 ~10 mins complete uninstallation
¶ On CyberGateway terminal using command line
To uninstall CyberGateway from CyberGateway system directly
- SSH to CyberGateway
- type “sudo -s” to switch to root
- Run following command on terminal to uninstall
cgw uninstall